 Ruby: Deploy with GitHub Actions
Ruby: Deploy with GitHub Actions
How to deploy your Ruby code using GitHub Actions
👋 Welcome to the Stackhero documentation!
Stackhero offers a ready-to-use Ruby cloud solution that provides a host of benefits, including:
- Deploy your application in seconds with a simple
git push.- Use your own domain name and benefit from the automatic configuration of HTTPS certificates for enhanced security.
- Enjoy peace of mind with automatic backups, one-click updates, and straightforward, transparent, and predictable pricing.
- Get optimal performance and robust security thanks to a private and dedicated VM.
Save time and simplify your life: it only takes 5 minutes to try Stackhero's Ruby cloud hosting solution!
GitHub Actions allows you to automate tasks such as deploying your Ruby code to production servers.
In this guide, you will learn how to securely and reliably use GitHub Actions to deploy your Ruby code to both staging and production environments.
To achieve this, you will maintain two branches: staging and production, where code pushed to these branches will automatically be deployed to the corresponding Stackhero instance.
Having a staging instance is not mandatory. You can follow this guide and have just one production instance. However, to ensure smooth deployments and be fully confident when deploying to production, it is strongly recommended to maintain both a staging and a production instance. This practice is an industry standard and a good practice, helping you avoid numerous issues.
To proceed with this guide, you need a GitHub account with a repository hosting your code.
Creating the Ruby services
Go to your Stackhero dashboard and create two Stackhero services, one for staging and one for production. To avoid any confusion, we recommend renaming these services to "Production" and "Staging".
Don't have a Stackhero account yet? You can create one in just two minutes, for free, and then create your Ruby cloud services with just a few clicks.
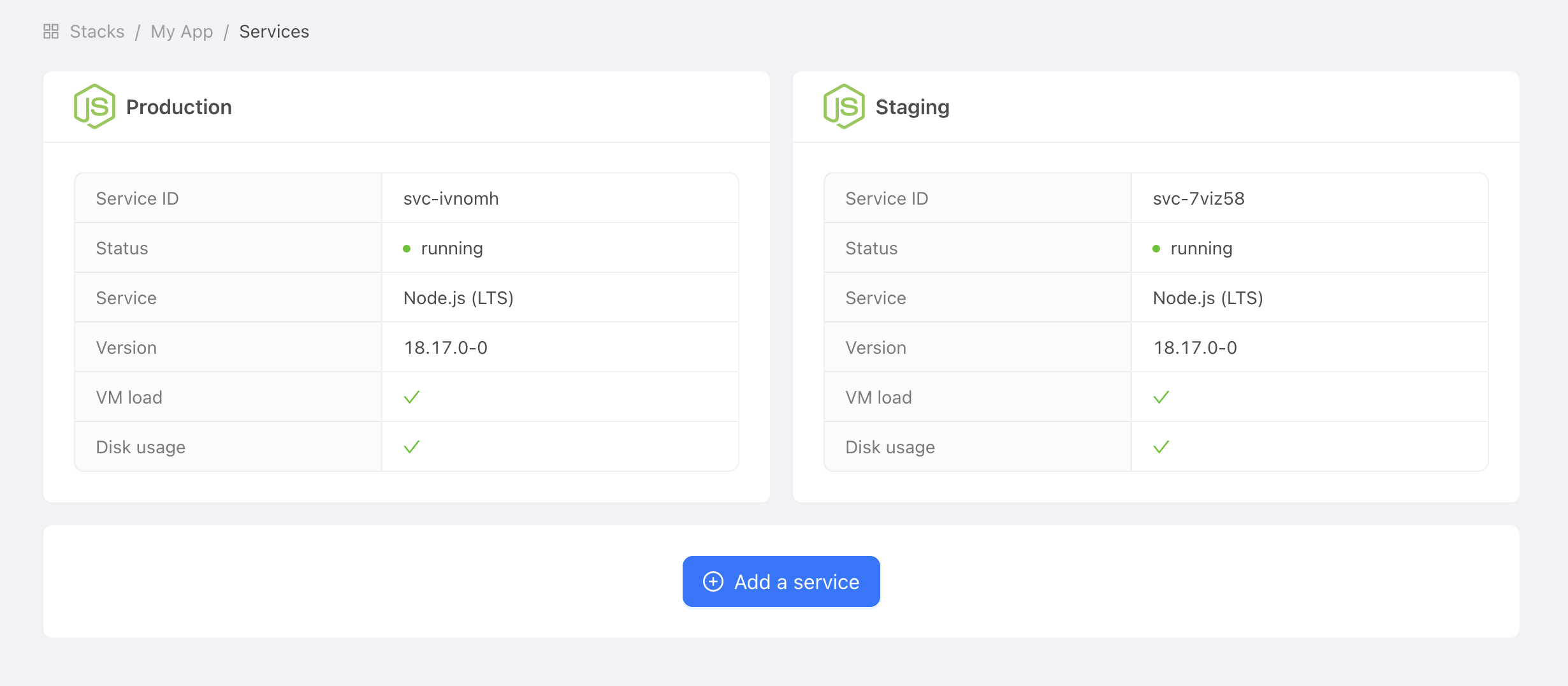 Example of production and staging services
Example of production and staging services
Configure SSH keys
SSH keys will give GitHub Actions the right to connect to your Ruby service to deploy your code. This is an essential part of securing your Stackhero services.
On your computer, create new SSH keys:
ssh-keygen -C "" -f /tmp/ssh_key -N ""
Set the public key
Retrieve the public key you just generated:
cat /tmp/ssh_key.pub
In Stackhero's dashboard, select your "production" Ruby service and click on the "Configure" button.
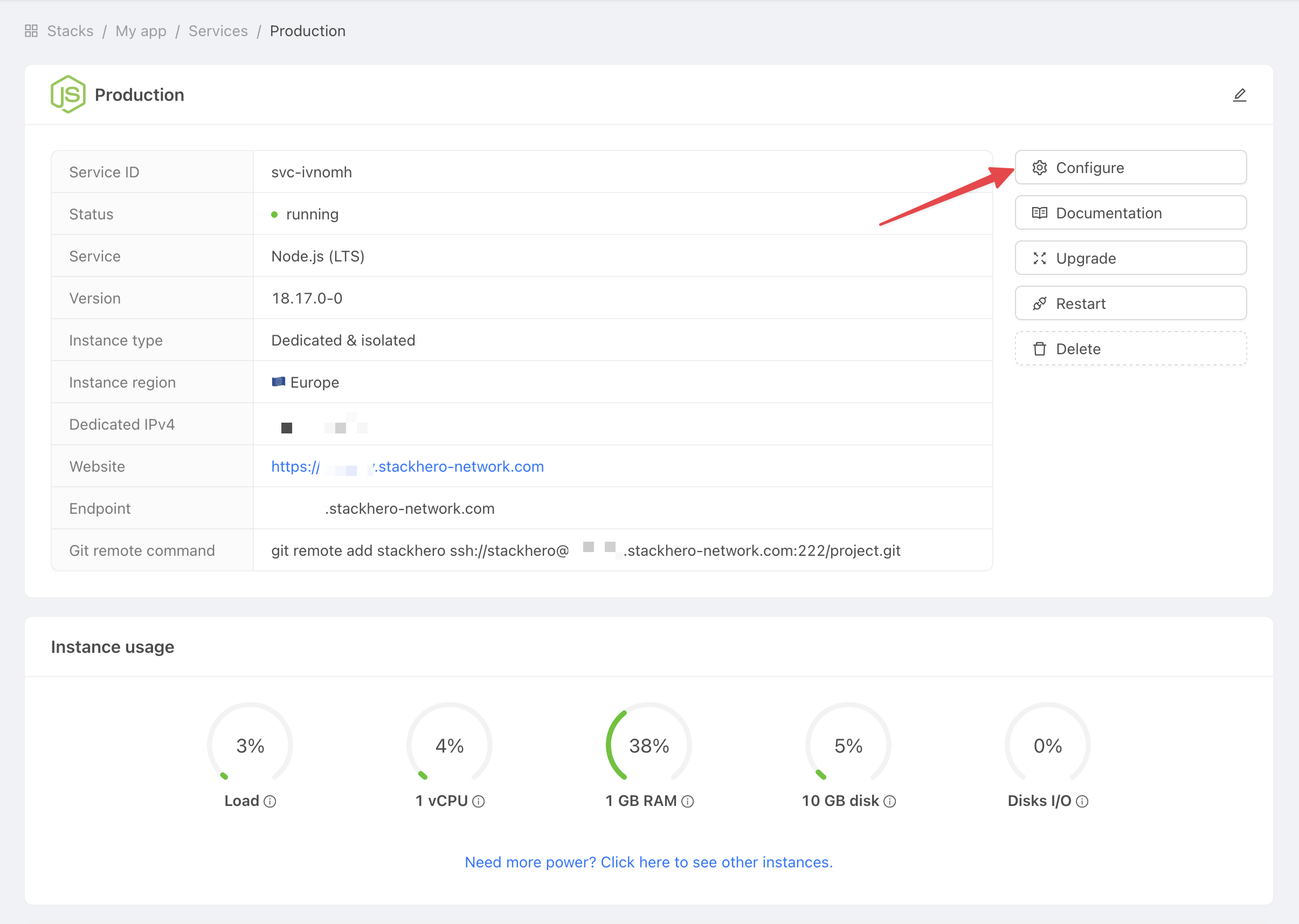 Get service settings
Get service settings
Then:
- In
SSH public keys, click onAdd a public key. - In
Description, setGitHub Action. - In
Key, paste the content of the public key you have on your computer.
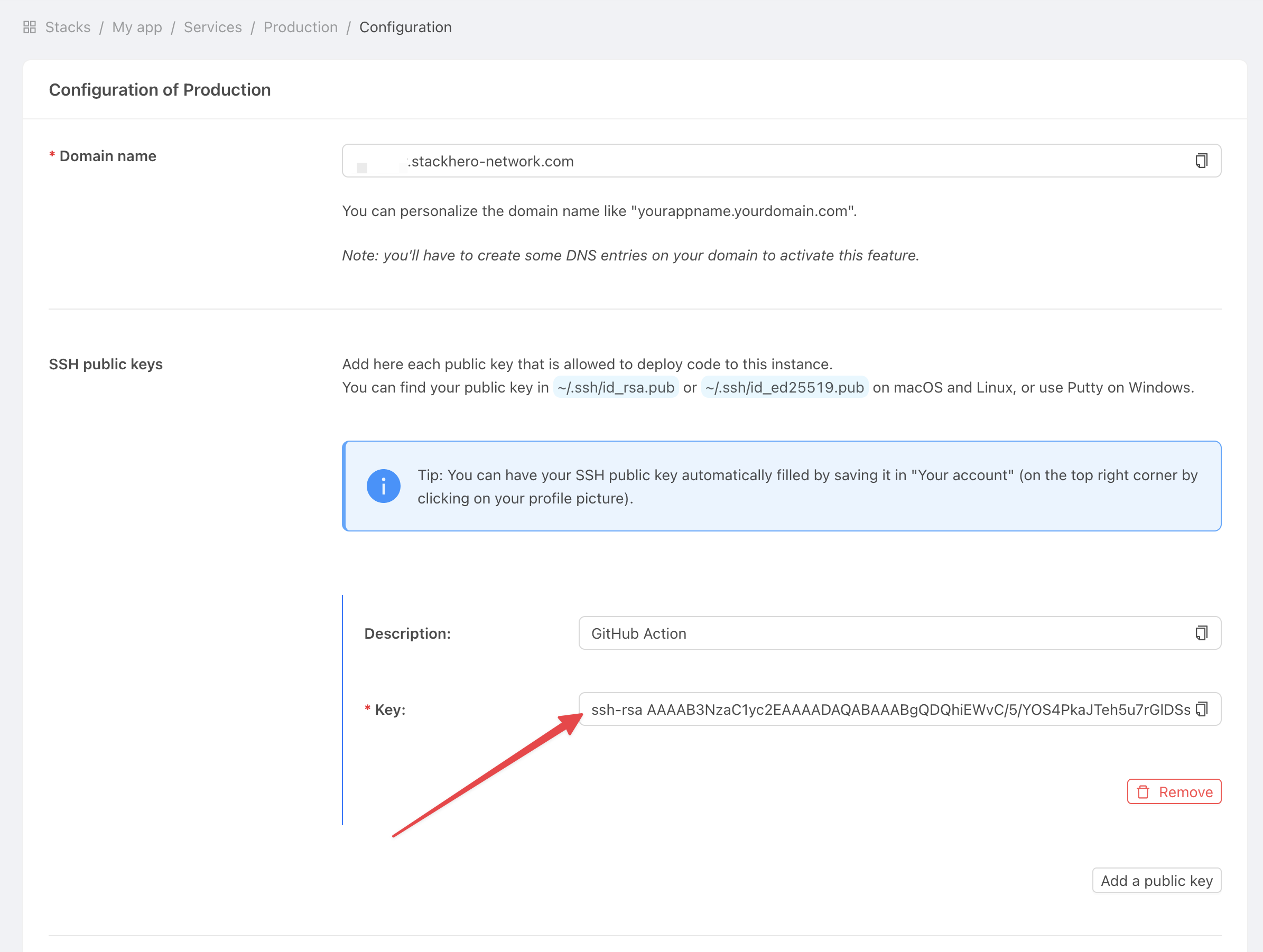 Get service settings
Get service settings
Set the private key
Go to the GitHub website and select your project.
Click on Settings/Environments and then on New environment.
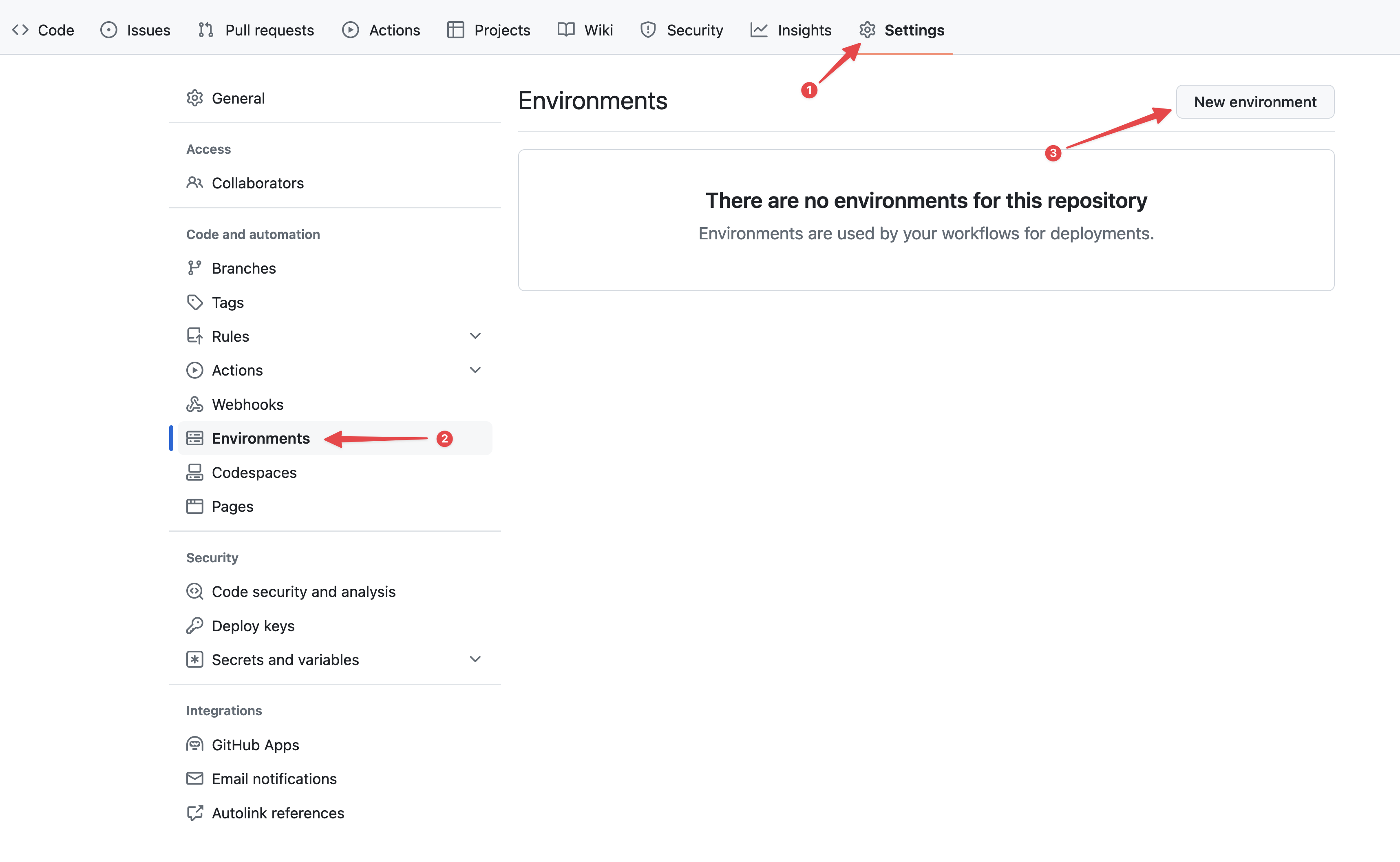 Configuring GitHub environments
Configuring GitHub environments
In Name, set "production" and confirm.
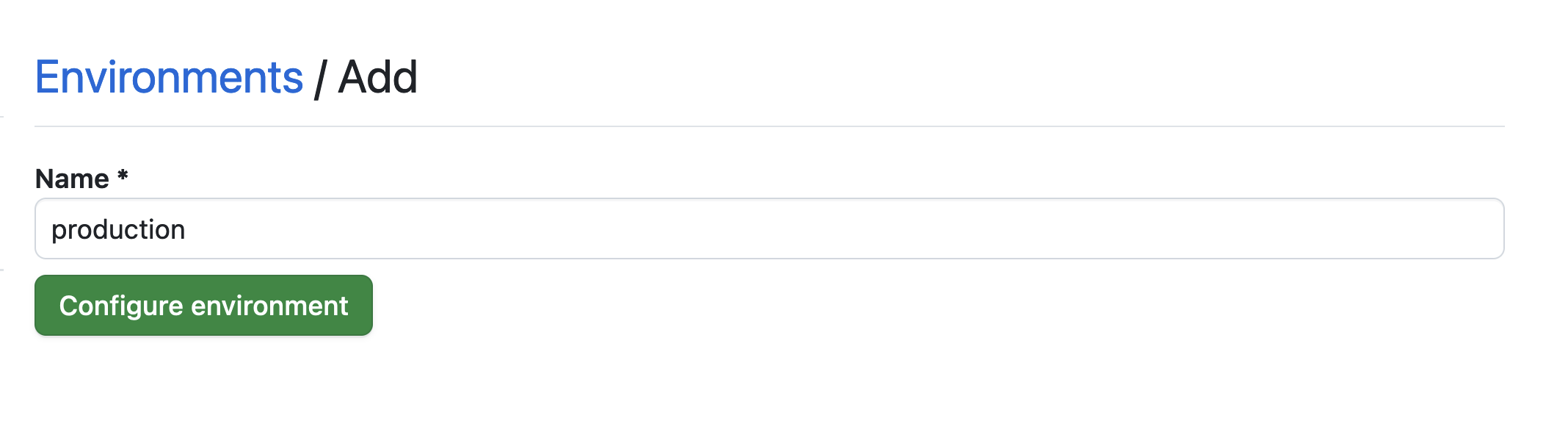 Setting the environment
Setting the environment
Click on the No restriction button and select Selected branches and tags.
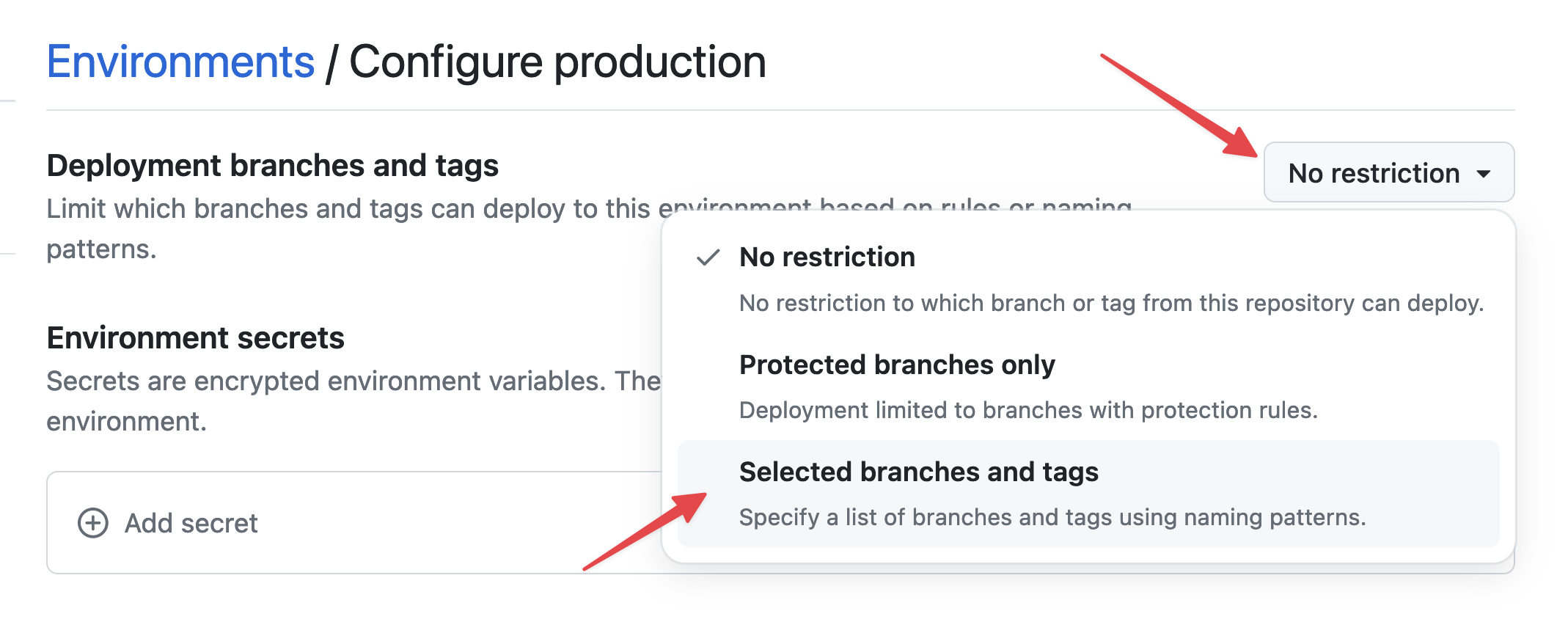 Setting environment restrictions
Setting environment restrictions
Click on Add deployment branch or tag rule, enter "production" in Name pattern, and click on Add rule.
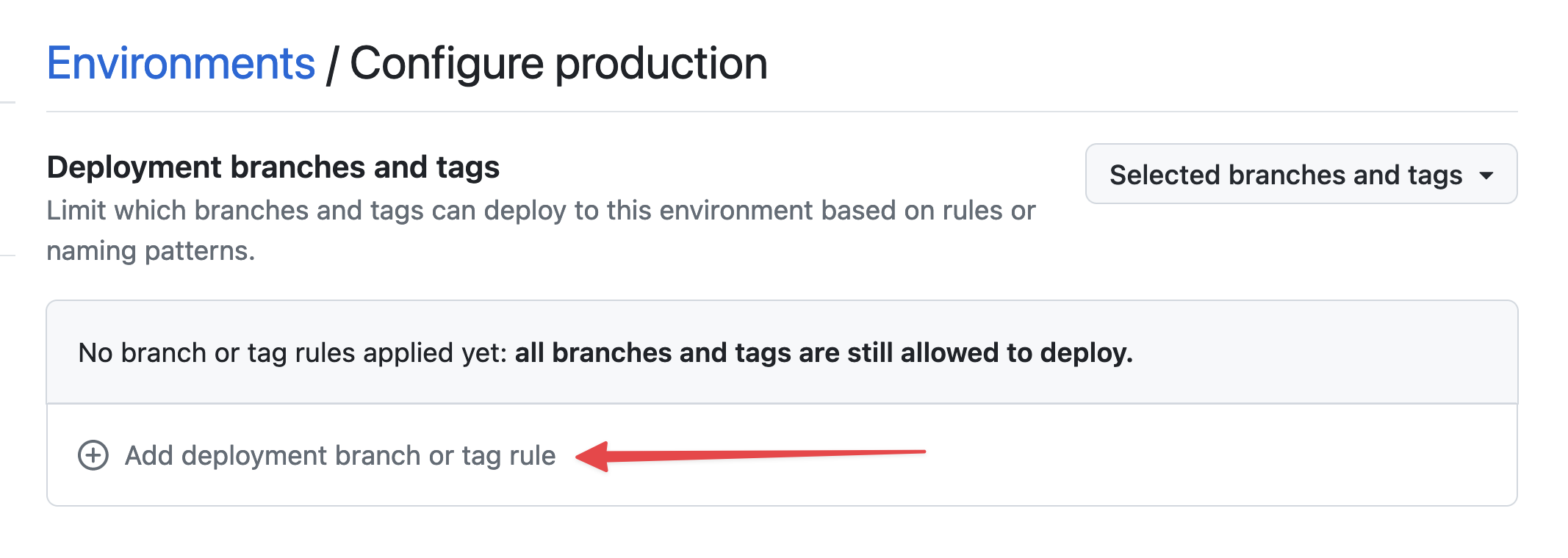 Setting environment branch
Setting environment branch
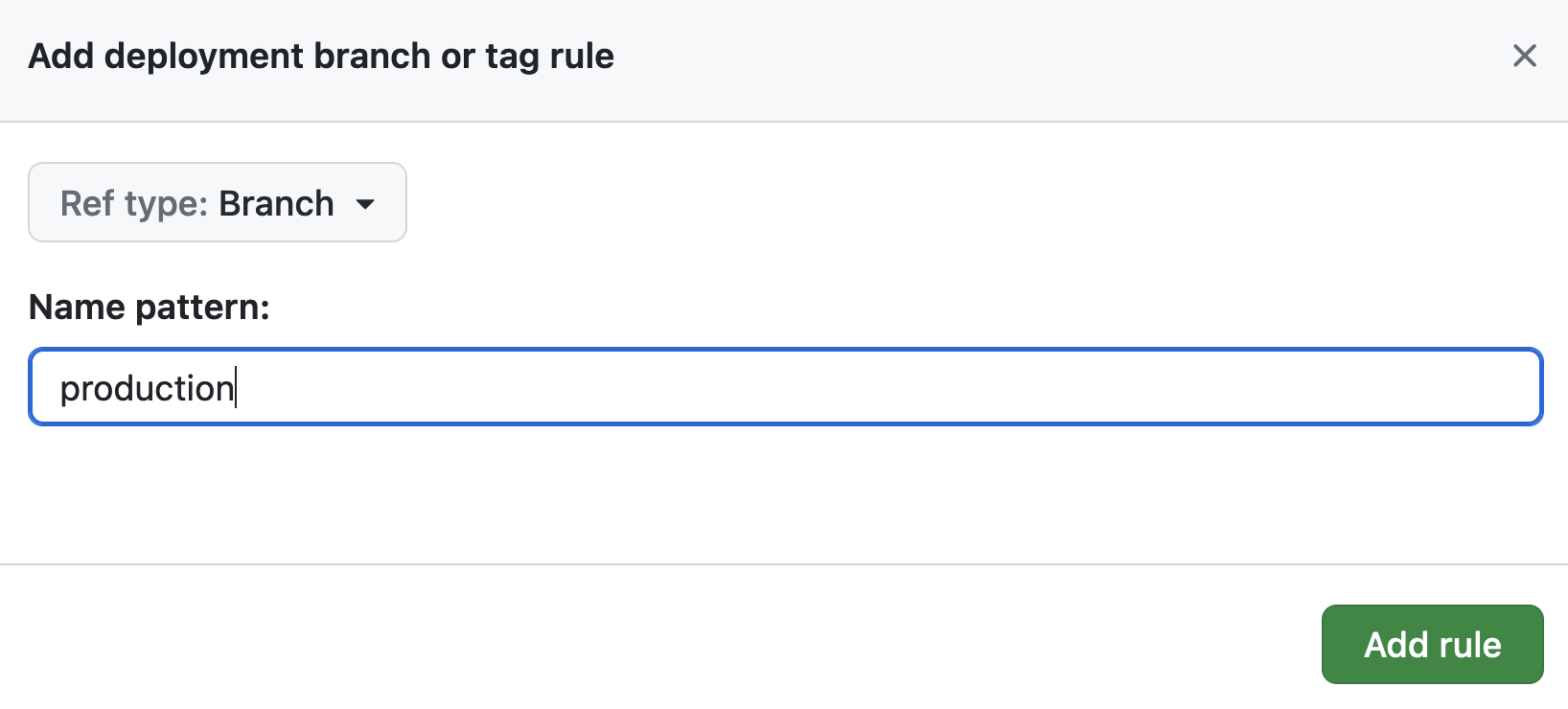 Setting environment branch
Setting environment branch
In Environment secrets, click on Add secret.
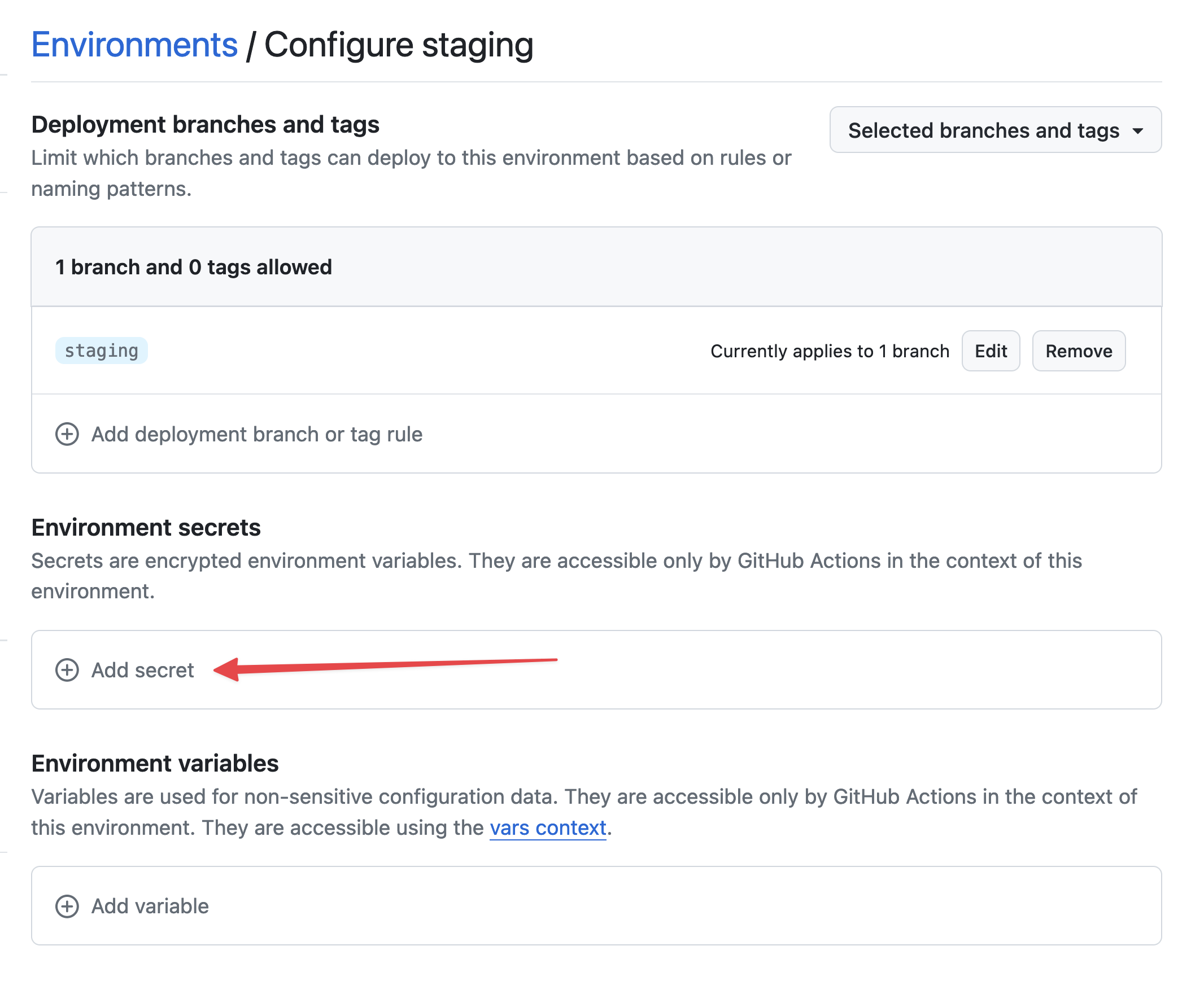 Add secret
Add secret
Retrieve the private key you previously generated on your computer:
cat /tmp/ssh_key
In Name, put STACKHERO_SSH_PRIVATE_KEY. In Value, paste your private key.
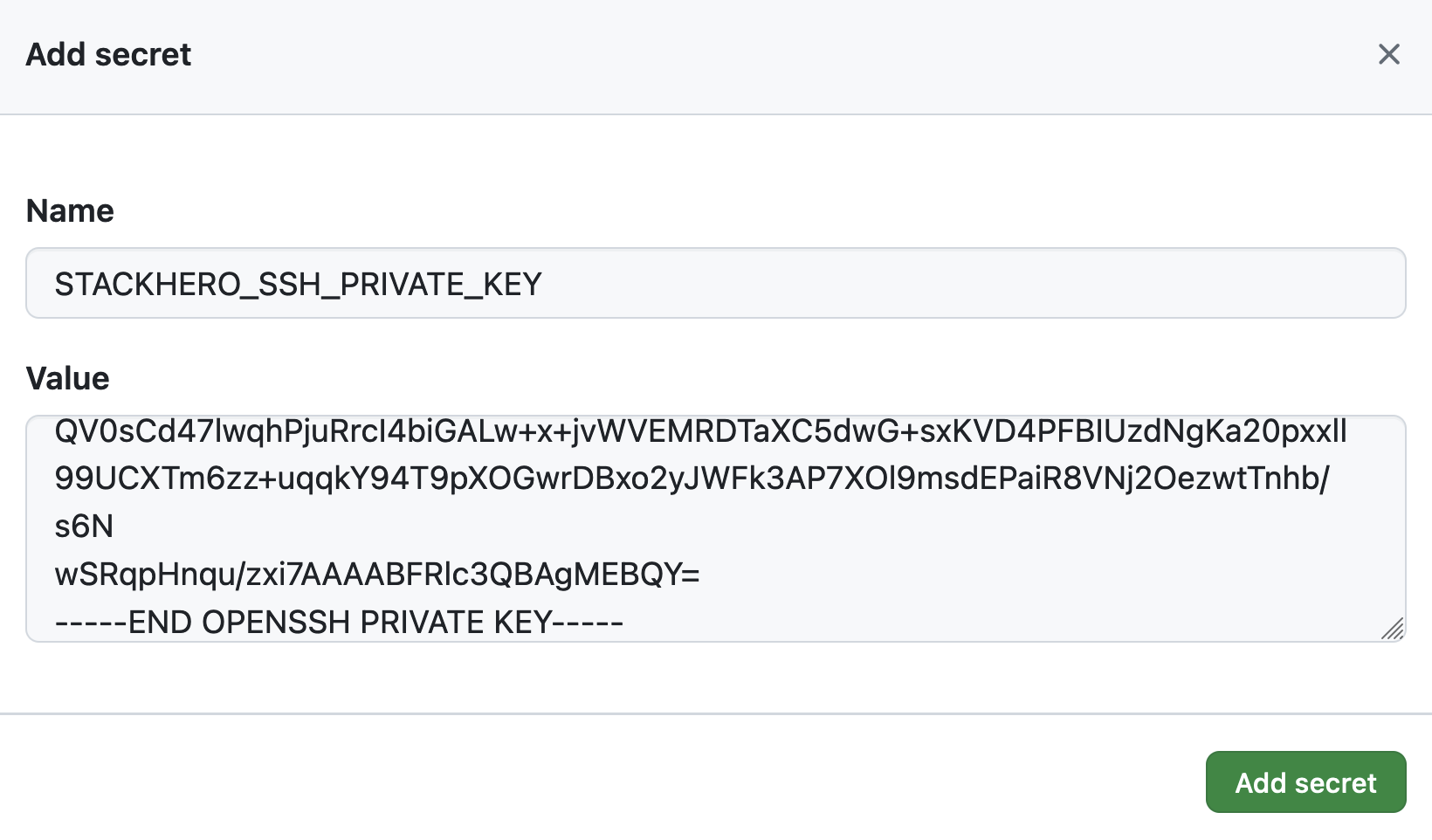 Setting the SSH private key secret
Setting the SSH private key secret
In Environment variables, click on Add variable.
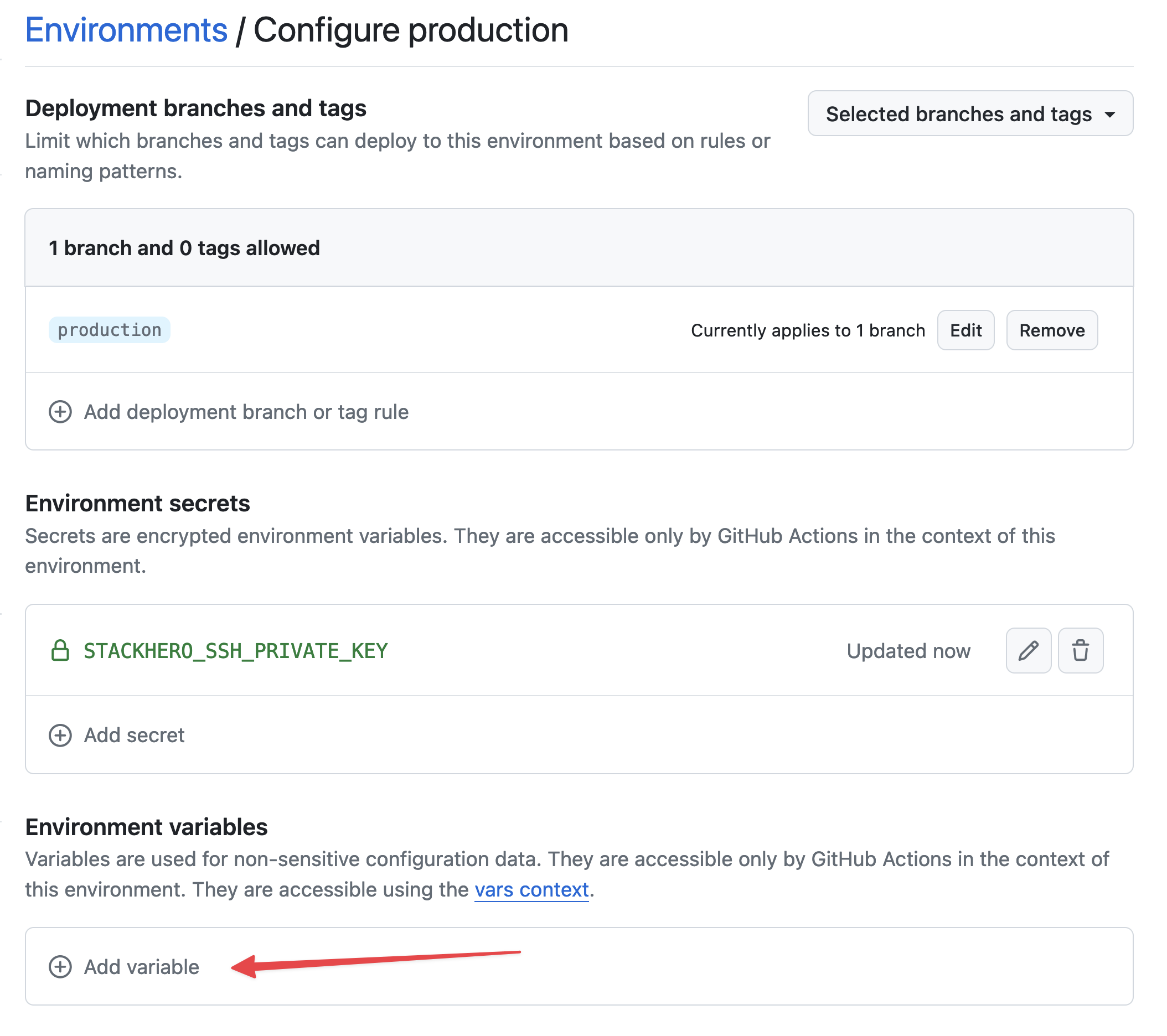 Setting variables
Setting variables
In Name, put STACKHERO_ENDPOINT. In Value, paste your Ruby service endpoint. You will find it in your Stackhero dashboard.
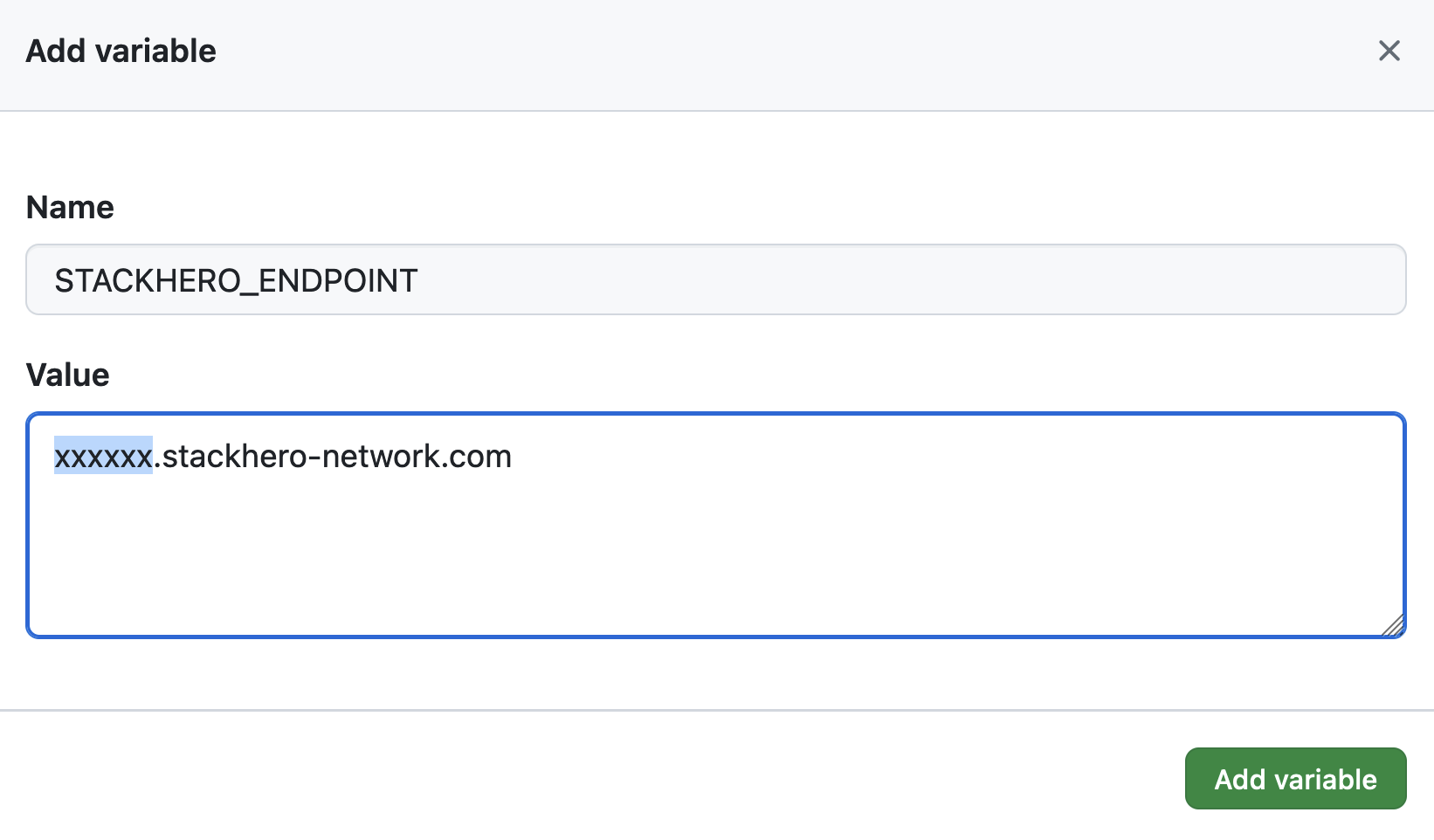 Setting the endpoint variable
Setting the endpoint variable
If you have customised your service's domain name, use the customised version instead of xxxxxx.stackhero-network.com.
Delete the generated keys
Since you will no longer need the previously generated SSH keys, you can delete them from your computer for security reasons:
rm /tmp/ssh_key /tmp/ssh_key.pub
Configure the GitHub Actions workflow
In your Git repository, on your computer, create a directory called .github/workflows.
In this directory, create a file named deploy-to-stackhero.yml.
# File: .github/workflows/deploy-to-stackhero.yml
name: Deploy to Stackhero
run-name: Deploy branch "${{ github.ref_name }}" to Stackhero
on:
push:
# List of branches that will trigger the deploy action following a git push.
# Don't forget to create an environment corresponding to the branch name in GitHub (in "Settings"/"Environments").
# Then add the corresponding secret "STACKHERO_SSH_PRIVATE_KEY" and variable "STACKHERO_ENDPOINT" in this environment.
branches: [ "production", "staging" ]
jobs:
Deploy:
environment: ${{ github.ref_name }}
runs-on: ubuntu-latest
steps:
- uses: stackhero-io/github-actions-deploy-to-stackhero@v1
with:
# The secret "STACKHERO_SSH_PRIVATE_KEY" and the variable "STACKHERO_ENDPOINT" should be defined in the corresponding branch environment on GitHub under "Settings"/"Environments".
ssh_private_key: ${{ secrets.STACKHERO_SSH_PRIVATE_KEY }}
endpoint: ${{ vars.STACKHERO_ENDPOINT }}
Commit your changes:
git add -A .
git commit -m "Add GitHub Actions to deploy to Stackhero"
Then create a production branch:
git checkout -b production
Finally, push your changes to GitHub:
git push --set-upstream origin production
This final git push command will push the code from your computer to the GitHub branch production. GitHub Actions will automatically run and deploy this code to your Stackhero instance.
To check this action, go to the GitHub website, select your project, and click on Actions.
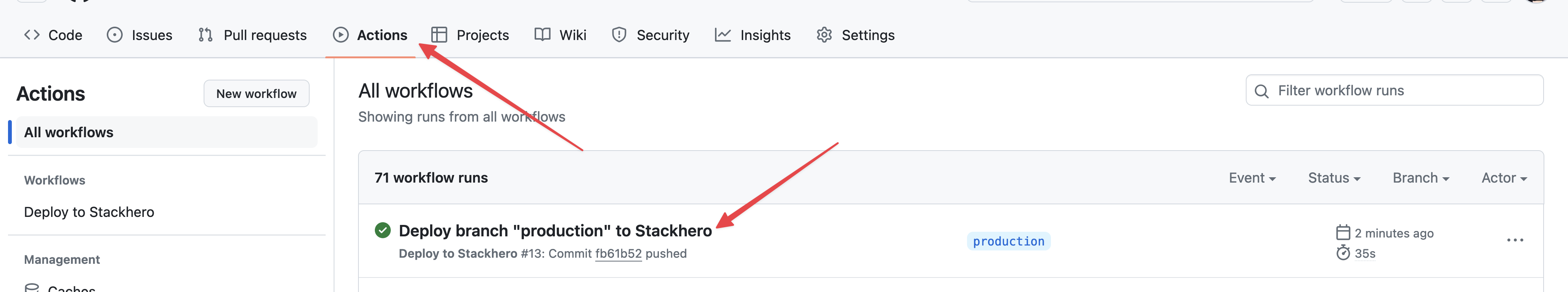 GitHub Actions that deployed to production
GitHub Actions that deployed to production
Congratulations, you can now automatically deploy your code to production via GitHub Actions!
Creating the staging environment
Creating the staging environment is similar to setting up the production environment.
To create it, repeat the steps from the previous sections of this guide, simply replacing production with staging.
Then create a staging branch:
git checkout -b staging
Finally, push your changes to GitHub:
git push --set-upstream origin staging
GitHub Actions will automatically deploy your staging branch to the Ruby instance designated for staging.
Going further
A good practice is to protect the production and staging branches to prevent direct pushes to them.
In this case, a pull request must be created for the staging branch and then merged by people with the rights to push code to staging.
Once validated on the staging platform, the pull request can be merged into the production branch by the same people who have the rights.
This approach ensures security (only authorised people can push to staging and production) and reliability (new features are tested on a staging platform first before being pushed to the production branch).